If you have always been interested in privacy and hacking in a good way, you may have heard of Metasploit. It can be used in many different ways. This powerful tool is the go-to for security workers and enthusiasts who want to find vulnerabilities, rate system security, and run thorough tests. You’re in the right place if you want to run Metasploit in Termux, which is a popular Linux terminal emulator for Android. In this step-by-step guide, we’ll show you how to get the most out of Metasploit on an Android device.
Table of Contents
How do I install Metasploit in Termux?
Metasploit is a lighthouse for security experts in a digital age where cybersecurity worries are common. Metasploit is a free penetration testing program that lets you use a set of tools to test the security of computer systems. It’s more than a tool; it’s a partner in the fight against security holes because it lets you run attacks and see what could happen after a hack.
Prerequisites for Installation
Make sure a few things are in place before you start downloading:
- A ready-to-go Android gadget that works.
- A link to the internet that works well.
- How the command line works in general.
Setting up Termux: Your Playground for Linux
Setting up Termux, which gives you access to a Linux-like environment on your Android device and is the first step in installing Metasploit, is the next step. Here’s how you should begin:
- You can get Termux from the Google Play Store.
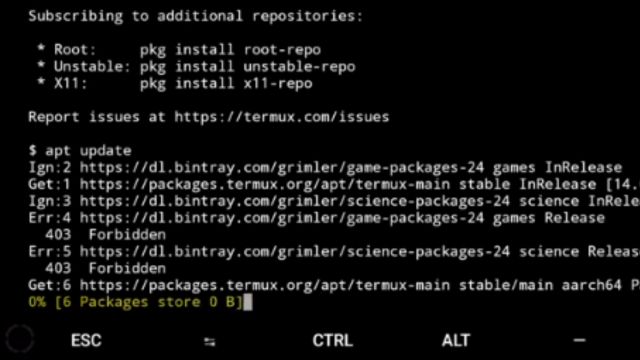
- Once Termux is running, type the following command to update and upgrade packages:
apt install sql and update
The Steps For Installing Metasploit
You need to take a number of well-thought-out steps for Metasploit to work on your Android device. Here is how to do it:
- First, use sql pkg update to change the package source.
- When you type pkg install wget, the wget package will be put in place.
- To protect the Metasploit script, type: bash wget https://raw.githubusercontent.com/Hax4us/Metasploit_termux/master/metasploit.sh.
- If you type bash +x chmod metasploit.sh, the script will be able to run.
- To set up, run the bash./metasploit.sh tool.
- Do what the software tells you to do to finish the process.
Configuration: Fine-Tuning Metasploit for Your Needs
After you start Metasploit, the next step is to set it up. With the command msfconsole, you can start up the Metasploit interface.
Find out the most important Metasploit tools and how to use them.
For Metasploit to work, you have to know the basic commands:
- When this code is run, the Metasploit interface starts up.
- search keyword>: This lets you look for modules by phrase.
- choose module: Picks a certain module to abuse.
Digging Deeper: Exploring the Array of Modules
Metasploit is what it is because it is made up of many different parts. These lessons talk about different parts of penetration testing, like screening, exploiting, and what to do after an attack. Use the search feature to find tools that will help you reach your goals.
Payloads Unveiled: Crafting Your Digital Arsenal
The payloads are the most important part of Metasploit. With these, you can send carefully written code to systems that need it. With the msfvenom app, you can make payloads that are just right for your goals.
The Art of Exploitation: Executing Your Plans
Metasploit makes it easier to break into weak systems. After choosing a good exploit module, set up the necessary choices and let the exploit command do its thing.
Beyond the Hack: Post-Exploitation Techniques
Metasploit is more than a hacker tool. It has parts that are made to gather information, switch to different systems, and keep access to settings that have been hacked.
Metasploit Community and Resources: Joining the Tribe
When you join the Metasploit group, you can use a lot of tools. Meet other people who are interested in ethical hacking, hear talks, and find out what’s new in the world of ethical hacking.
Navigating Ethical Quandaries and Legal Considerations
Metasploit is a strong friend, but with strength comes the need to be responsible. The most important thing is that you use it well and legally. Before you start any security tests, make sure you have the right permissions.
Troubleshooting the Labyrinth: Common Challenges
With Metasploit, things might not always go smoothly. If you’re having trouble, you can find answers and help in the official documentation and the busy community boards.
Unlocking Effectiveness: Tips for Optimal Utilization
- Keep Metasploit and its tools up-to-date so you can use the latest features.
- You should know what a lesson is about before you start using it.
- Make sure you practice somewhere safe so that nothing bad happens by chance.
Conclusion
When Metasploit is added to Termux, it opens up a lot of new options for people who are interested in safety. With this powerful tool, users can test systems, find weak spots, and improve security as a whole. Don’t forget that with this kind of power comes a lot of duties. Metasploit should only be used when there is a good and legal reason to do so. To read more content like this, visit https://www.trendblog.net.
Frequently Asked Questions (FAQs)
Is it true that only skilled hackers can use Metasploit?
Metasploit is good for people of all skill levels, from those who are just starting out to those who know a lot. It can be used to learn and by pros as a guide.
Metasploit can be put on Android, but can it also be put on other computers?
Metasploit can be used on computers that run Windows, Linux, or macOS.
Is Metasploit the only thing?
In fact, Cobalt Strike and OWASP Zap can be used to check for security holes, just like Metasploit.
Can you get in trouble with the state if you use Metasploit?
Metasploit can be used legally when checking for security holes. But it is against the law to use it for bad things without the right permission.
Where can I learn more about Metasploit’s more complicated parts?
Look at the official literature and web tutorials to find out how to use Metasploit in more complicated ways.