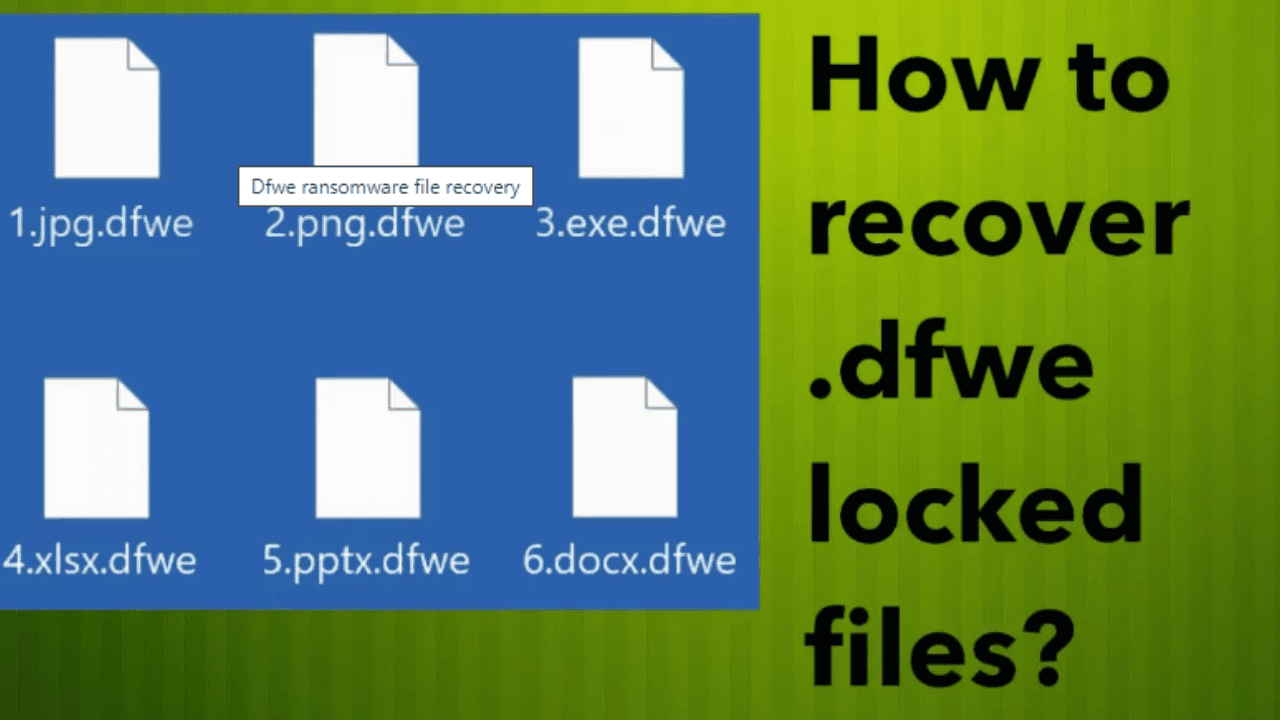
The dfwe File Virus is a ransomware strain that was developed to steal money from unwitting computer users. The dfwe File Virus is a ransomware that is so aggressive that it may break the system and lock up all user data. Every time you boot up your computer, the dfwe File Virus will display a pop-up warning saying that your files have been encrypted and that you must pay bitcoins to decrypt them.
In general, a variety of criteria can be used to explain why a computer became infected with the dfwe File Virus. This fraud can be started by clicking a malicious link, a spam email attachment, or a pornographic website. Additionally, the most frequent methods utilized by the dfwe File Virus to effectively enter a computer include a portable device and the ramsomlock Trojan horse. Now, let’s find out how to recover .dfwe locked files.
Table of Contents
Steps to recover .dfwe locked files
Kill Dfwe virus
Tap Task Manager. Look for anything suspicious that may be the Dfwe ransomware, then right-click it and choose “End Task” or “End Process” from the menu that appears. The following instructions should be followed if your Task Management won’t launch or Windows says “Task manager has been deactivated by your administrator.” How to Fix Your Administrator has deactivated Task Manager.
Finding a process connected to the Dfwe ransomware is simple. Be mindful of the process icon and name when searching for harmful processes. This malware often has a process name that looks like this: Alternatively known as 4-characters.tmp.exe. Examples include A4b1.exe, CD15.tmp.exe, 19b2.exe, and 7533.tmp.exe. “(32-bit)” may also appear in the process name. If there isn’t a process with a similar name in the list of running processes, the Dfwe ransomware is probably done. But bear in mind that if you do not eliminate the ransomware’s autostart entries, as shown below, and do not destroy its file, it may restart after a time and encrypt any unencrypted files it discovers.
Disable Dfwe Startup
Look for anything like the one in the example below under the “Start-Up” tab, right-click on it, and choose Disable. Shut off Task Manager.
Delete Dfwe Task
The search bar should be set to “Task Scheduler.” In the list of search results, select Task Scheduler app. In the left side, click “Task Scheduler Library”. Right-click “Time Trigger Task” on the right panel and choose “Delete.”
Remove Dfwe virus
Start Task Manager, then choose the “Start-Up” tab. As illustrated below, right-click the Dfwe ransomware Start-Up item and choose Open File Location.
You’ll see the Dfwe virus file in a directory that has just one file in it. It must be taken out. It is protected against deletion, so if you try to delete it right away, you won’t be successful.
You must carry out the following in order to remove this file. Property may be accessed by right-clicking the file. Pick the Security tab in the newly opened window. Click the Advanced option below after that. The following example will demonstrate how a window will open.
To turn off inheritance, click. Choose the first option (Convert inherited permissions…) in the Block inheritance dialogue box that appears, as shown below.
Select “Deny Everyone” from the list of permission entries, then click the Remove button and OK to finish. Close the window for file properties. The Dfwe virus ought to be easy to eliminate at this point. Simply choose to Delete with a right-click on the file.
Also Read
How to fix Windows 10 update error code 0x800f0831?
How To Recover Lost Text Messages On An iPhone Or Android Phone
What are the prerequisites to Install a Custom ROM in your Android?
How to Root Kindle: Problem while Rooting
FAQs
Q. How to find out the type of a key using ‘_readme.txt’ file
- Open the ransom demand message (‘_readme.txt’ file).
- Scroll down to the end of the file.
- There you will see a line with the text ‘Your personal ID’.
- Below is a line of characters – this is your personal id.
Q. How to find out the type of a key using the ‘PersonalID.txt’ file
- Open disk C.
- Open the directory ‘SystemID’.
- The open file is named ‘PersonalID.txt’. This file lists Personal IDs that match the keys that the virus used to encrypt files.
The ‘Personal ID’ is not a key, it is an identifier related to a key that was used to encrypt files. If the ID ends with ‘t1’, then the files are encrypted with an offline key. If the ID does not end with ‘t1’, Dfwe virus used an online key. If you could not figure out how to determine which key was used to encrypt files, then we can help. Just write a request here or in the comments below.
Q. How to protect your computer from Dfwe ransomware
Most antivirus programs already have built-in protection systems against crypto-malware. Therefore, if your computer does not have an antivirus application, make sure you install it. As extra protection, run the HitmanPro.Alert. All-in-all, HitmanPro.Alert is a fantastic utility to protect your computer from any ransomware. If ransomware is detected, then HitmanPro.Alert automatically neutralizes malware and restores the encrypted files. HitmanPro.Alert is compatible with all versions of the Windows operating system from Windows XP to Windows 10.
Visit the following page to download HitmanPro Alert. Save it to your Desktop so that you can access the file easily.


Comments are closed.