You must have come through a ransomware attack. It is quite frequent. Because all the processes connected to this virus can cause issues with applications, functions, and data, ransomware infestations are generating major problems with the computer. While the Qlln ransomware primarily locks and encrypts files, there are other issues with the cryptovirus infestation.
Due to the fact that the majority of virus developers have financial interests, these threats are predicated on bitcoin extortion. The invasion may be quite quiet, and the problem with locked files manifests before any system flaws or sluggish performance. It’s because malware might suddenly surface and start encoding files.
Once the ransomware payload is delivered to the system, the file virus is capable of immediately locking the frequently accessed data.
Now, if you want to know more about how to recover your files, keep reading!
Table of Contents
What is Qlln ransomware?
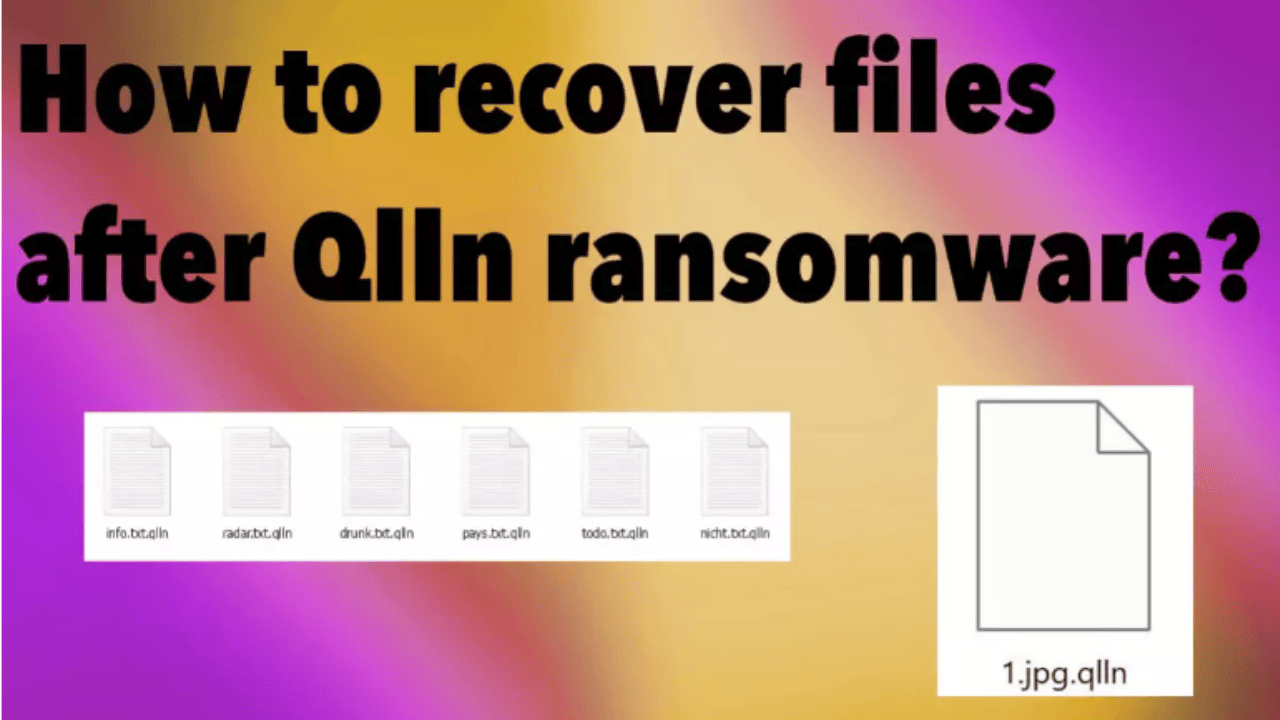
Security experts claim that Qlln is a malware designed to encrypt data. This virus is therefore a member of the “ransomware” family. This particular kind of malware is intended to encrypt data and then demand a ransom to unlock it. The Qlln virus renames files after encrypting them and adds the.qlln suffix. For instance, a file with the name “photo.jpg” will become “photo.jpg.qlln” after encryption, whereas a file with the name “document.doc” will become “document.doc.qlln,” and so on. The virus produces a file called “_readme.txt” that contains a message from the authors of this harmful program when the encryption procedure is finished.
Steps to recover files after Qlln ransomware
Decrypt the locked files
The Qlln ransomware and other new variations of the Djvu ransomware virus family are currently among the most hazardous since they are frequently issued in groups of three or four. The threat is quite widespread, as evidenced by the abundance of samples and complaints from users and victims on the internet.
It also demonstrates how effective threats can be in getting programmers to alter the extension and release a new virus. These most recent modifications to the coding processes have aided these crooks in maintaining persistence and thwarting any potential virus decryption. These had previously been accessible due to offline id formation.
These most recent variants, like the Qlln ransomware itself, no longer encrypt using the offline keys. It implies that all keys—not just the malware file version—are available online and specific to a certain device. Individual online keys are needed for the decryption. The offline keys are never utilised if the connection to the C&C servers is stable. However, you should use the provided tool to look for the specific decryption option.
- Visit the official Emsisoft website to get the app.
- Click decrypt STOPDjvu.exe when it appears.
- Observe the directions on the screen.
- The impacted folders should be found by the utility.
- Additionally, you may do it by clicking Add folder at the bottom.
- Press
- There are particular results that can occur indicating if the decryption is possible.
Terminate the ransomware
These statistics may imply that ransomware is distributed using other malware as a vector since infections of different sorts can travel around utilizing a variety of techniques. The initial trojan and malware pieces that propagate via fraudulent platforms or spam emails and create no symptoms can spread infections like this Qlln ransomware.
Additionally, spam email attachments that include malicious macros and torrent websites that distribute software cracks, video game cheats, and other software packages with dangerous files already included can also be sources of ransomware invasion.
All of these infections can be concealed, and cryptovirus is one of the key dangers that call for effective anti-malware technologies, allowing for the prevention of all infection-related components. These AV tools can identify the Qlln file malware as well as associated threats and harmful files. Running a complete system scan with a reliable program can terminate the active malware and assist prevent further file locking.
Restore corrupted system data
- Install Reimage.
- Run the full system scan and wait for the complete analysis.
- Follow the on-screen steps.
- Allow the machine to get checked.
- Check the
- You can fix issues manually from the list.
- Purchasing a licensed version can help repair serious issues.
Recover the data with an app
- Get a tool like Data Recovery Pro from a trustworthy source.
- Follow installation instructions.
- Once that is finished, use the application.
- Select Everything or pick individual folders to recover.
- Press Next.
- Enable Deep scan at the bottom.
- Pick which Disk you want to be scanned.
- Hit Recover to restore files.
As of right now, the Qlln file virus’s official decryption tool has not been made public. Because researchers require certain keys and other information to create these programs, it takes a long time. Although there are other solutions, getting rid of the virus and stopping it from executing on the computer is the most crucial. You may securely recover data in this manner.
Also Read
How to Recover Deleted Videos From iPhone
How to Recover Permanently Deleted Photos from PC Using Wondershare Recoverit?
6 Best Ways to Recover Deleted Files on Windows 11/10
Free Methods To Put IPad In Recovery Mode
FAQs
Q. Can I recover files after a ransomware attack?
You cannot use File History or System Protection to restore data because some ransomware additionally encrypts or destroys backup copies. If that occurs, you must use backups on external discs, devices, or OneDrive as explained in the next
Q. What percentage of ransomware victims get their data back?
Only 42% said the payment resulted in the restoration of all systems and data (down from 51% last year. Furthermore, 54% said that system issues persisted or that some data was corrupted after decryption
Q. Should you pay the ransom for ransomware?
Most security and IT experts agree that there would be no need to pay the ransom if proper data backups were taken regularly. If you had backups readily available, you could simply restore your affected files and folders from this instead of paying the attackers


Comments are closed.